

Enabling SAML will affect all users who use this application, which means that users will not be able to sign-in through their regular log-in page. They will only be able to access the app through the Okta service.
Backup URL
Tehama provides the following backup log-in URL where administrators can sign-in using their normal username and password: https://[subDomain].tehama.io/login/organizationadminlogin, where [subDomain] is your Tehama subdomain value.
The Okta/Tehama SAML integration currently supports the following features:
For more information on the listed features, visit the Okta Glossary.
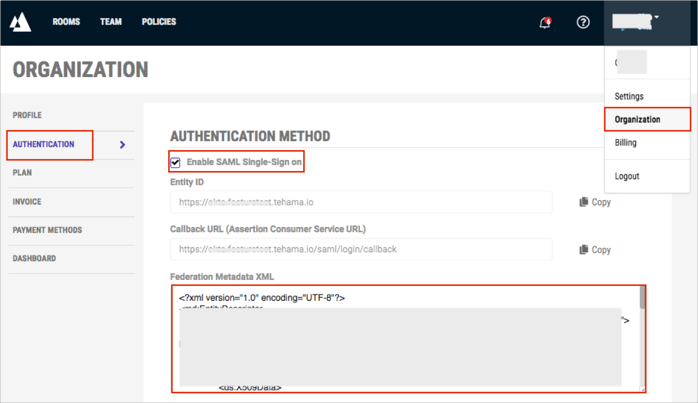
Login to your Tehama instance as an administrator.
Navigate to Account > Organization > AUTHENTICATION.
Check Enable SAML Single-Sign on.
Federation Metadata XML: Copy and paste the following:
Sign in to Okta Admin app to have this variable generated for you.
The next steps are optional and related to JIT (Just In Time) Provisioning.
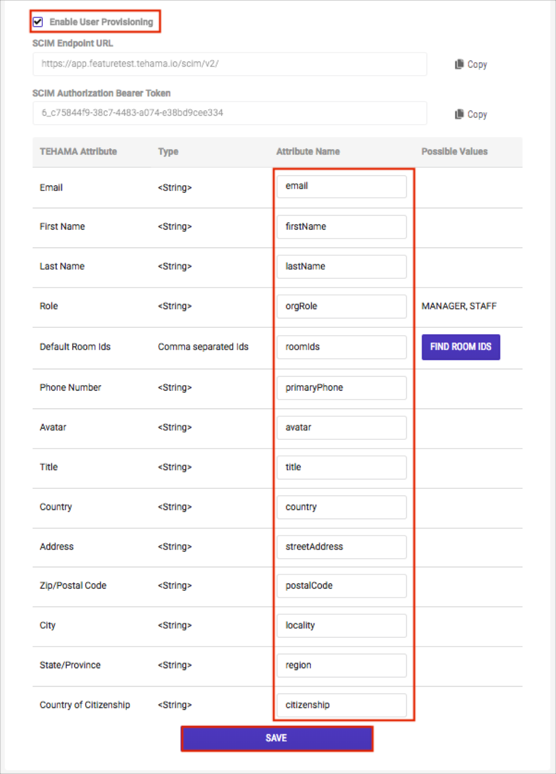
Check Enable User Provisioning.
Set the following mapping:
| TEHAMA Attribute | Attribute Name |
|---|---|
| First Name | firstName |
| Last Name | lastName |
| Role | orgRole |
| Default Room Ids | roomIds |
| Phone Number | primaryPhone |
| Avatar | avatar |
| Title | title |
| Country | country |
| Address | streetAddress |
| City | locality |
| Zip/Postal Code | postalCode |
| State/Province | region |
| Country of Citizenship | citizenship |
NOTES:
Email, First Name, and Last Name are mandatory for JIT. The rest of the attributes are optional. Optional attributes that not auto-provisioned will be given default values when the user is created and must be managed through the Tehama Web UI.
In order to use optional attributes you will need to add these attributes in the Okta application profile. Please follow the instructions in Adding Custom Attributes.
Notice the button FIND ROOM IDS in the Possible Values column for the entry for Default Room Ids. Click FIND ROOM IDS to bring up a dialog from which you can select Tehama Rooms from your organization. This produces a copyable comma separated value (CSV) string that you can use to populate the value of the custom attribute you added to the Okta application profile for Tehama room ids.
Click Save.
Done!
Make sure that you entered the correct Subdomain value under the General application tab in Okta. Using the wrong value will prevent you from authenticating via SAML to Tehama.
The following SAML attributes are supported:
Okta sends the following default attributes as part of the SAML assertion:
| Name | Value |
|---|---|
| firstName | user.firstName |
| lastName | user.lastName |
| user.email |
In addition to the default attributes, Okta supports the following custom attributes:
| Name | Value |
|---|---|
| orgRole | appuser.orgRole |
| roomIds | appuser.roomIds |
| primaryPhone | appuser.primaryPhone |
| avatar | appuser.avatar |
| title | appuser.title |
| country | appuser.country |
| streetAddress | appuser.streetAddress |
| postalCode | appuser.postalCode |
| locality | appuser.locality |
| region | appuser.region |
| citizenship | appuser.citizenship |
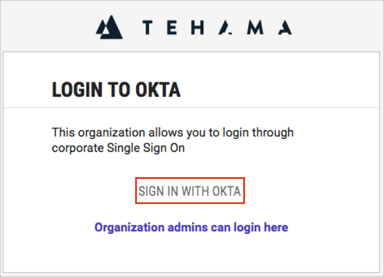
Open your organization login URL: https://[subDomain].tehama.io/.
Click SIGN IN WITH OKTA.
Here is an example describing how to add and use the additional title attribute:
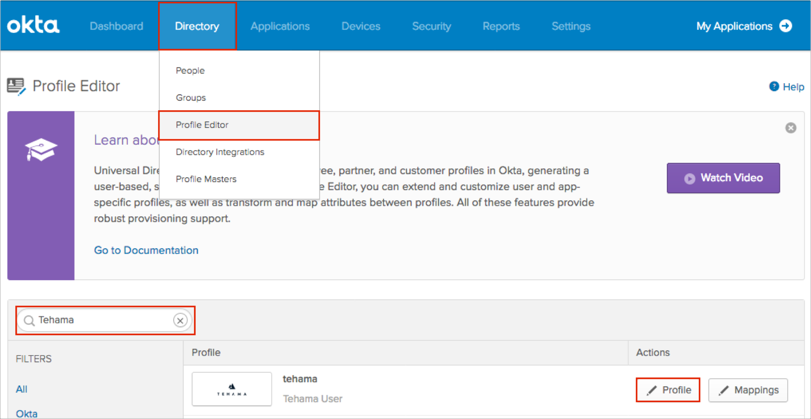
In Okta, navigate to Directory > Profile Editor:
Search for the Tehama app, then click Profile:
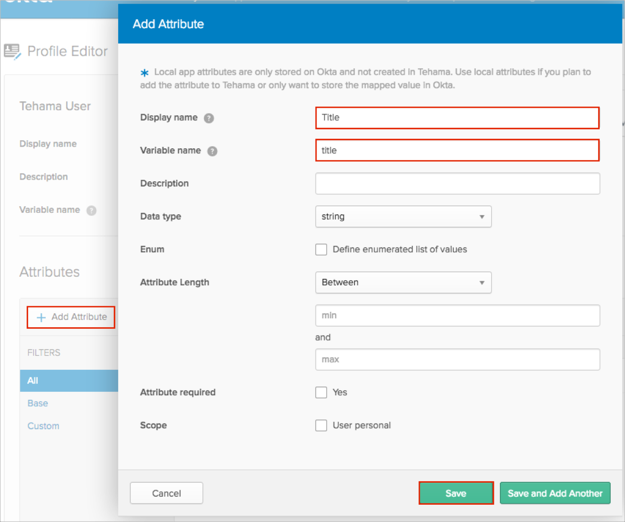
Click Add Attribute, then enter the following:
Display Name: Enter a preferred attribute name. In our example we used Title.
Variable Name: title.
Important: In our example we are adding the title attribute. You must use the following display / variable names (case-sensitive) for the custom attributes:
| Display name | Variable Name |
|---|---|
| Tehama Org Role | orgRole |
| Initial Room IDs | roomIds |
| Primary phone | primaryPhone |
| Avatar | avatar |
| Title | title |
| Country code | country |
| Street address | streetAddress |
| Postal Code | postalCode |
| Locality | locality |
| Region | region |
| Citizenship | citizenship |
The Tehama Org Role supports one of the following values: MANAGER or STAFF. Please use the following configuration for the attribute:
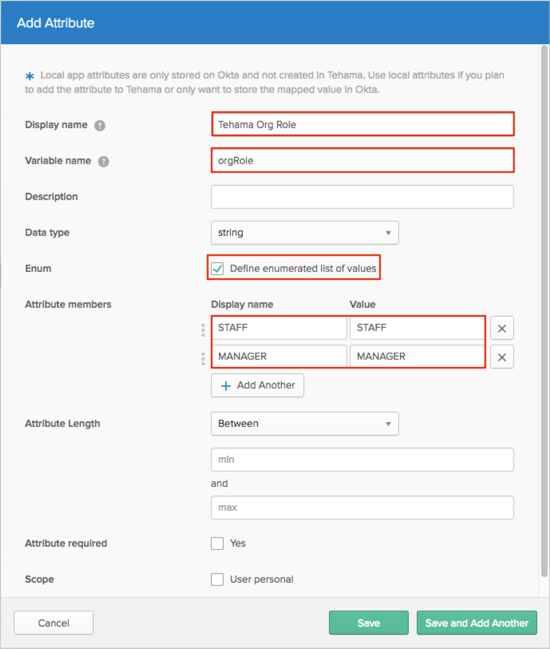
Click either Add Attribute or Save and Add Another.
Scope (optional): If you check User personal, it means that the current attribute will be available once you assign the user to the Tehama app and will not be available once you assign the Group to the Tehama app :
Click Map Attributes:
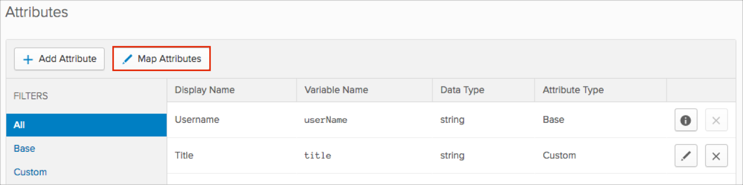
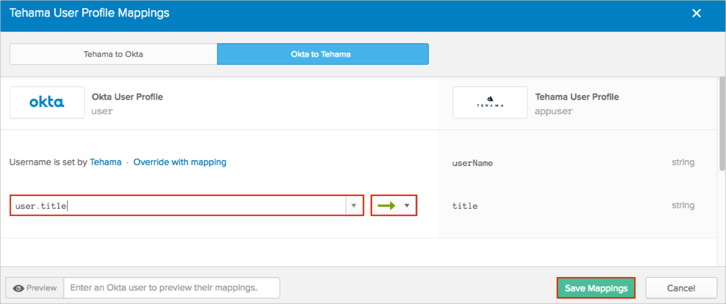
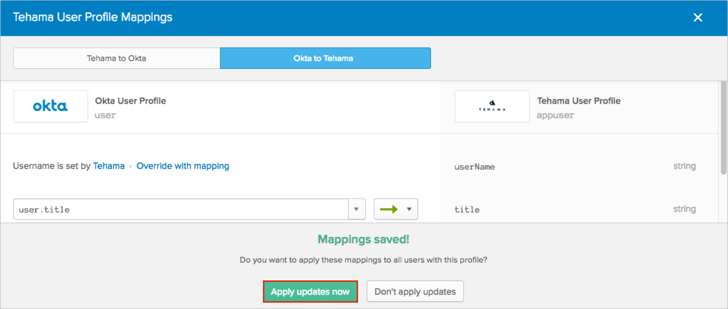
Select the Okta to Tehama tab.
Start typing the required attribute from the Okta Base User profile (or use the drop down list) and select the attributes you want to map.
In our example, we have selected the title attribute, and then use the green arrows (Apply mapping on user create and update).
Click Save Mappings:
Click Apply updates now:
Done!
Okta will now pass the title SAML attribute with the value of the title field from the Okta Base User Profile.