

Enabling SAML affects all users who use this application, which means that users will not be able to sign in through their regular log in page. They will only be able to access the app through the Okta service. However, users assigned the Super Administrator role can bypass SSO and log in directly to https://admin.google.com. We highly recommend creating a Suite Super Administrator account to allow for administrator access in the event SAML is no longer working properly.
If your Okta org already has a Google Workspace integration set up, skip step 1-4 of the Configuration Steps section. Simply add a new instance of the Google Cloud Platform app and proceed to step 5. This will only work if you are adding Google Cloud Platform to the same org where Google Workspace was set up.
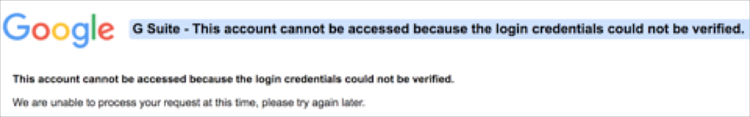
Note: If you encounter the following error after trying to access the GCP app that was added via this method, it may mean that your Google Workspace app instance was created before all Okta organizations were provisioned an additional 2048-bit self-signed X.509 Certificate:
To fix this issue, there are 2 solutions:
Upgrade your certificate:
Update the certificate for your existing Google Workspace application to a 2048-bit self-signed X.509 Certificate. This requires you to update your certificate in Google Workspace. Follow the instructions in this article: Updating SAML Certificate. After your certificate has been updated, your new Google Cloud Platform app should start working.
Clone/share an application certificate from the Google Workspace application to Google Cloud Platform application using the following instructions:
Add a Bookmark App:
Alternatively you can add a bookmark app that points to your Google Cloud Platform URL. To add a new bookmark app, follow this guide: Simulating an IDP-initiated Flow with the Bookmark App.
Note that the URL should be: https://www.google.com/a/[DOMAIN]/ServiceLogin?continue=https://console.cloud.google.com, where [DOMAIN] is your Google domain.
The Okta/Google Cloud Platform SAML integration currently supports the following features:
For more information on the listed features, visit the Okta Glossary.
Sign into your Google tenant using admin credentials.
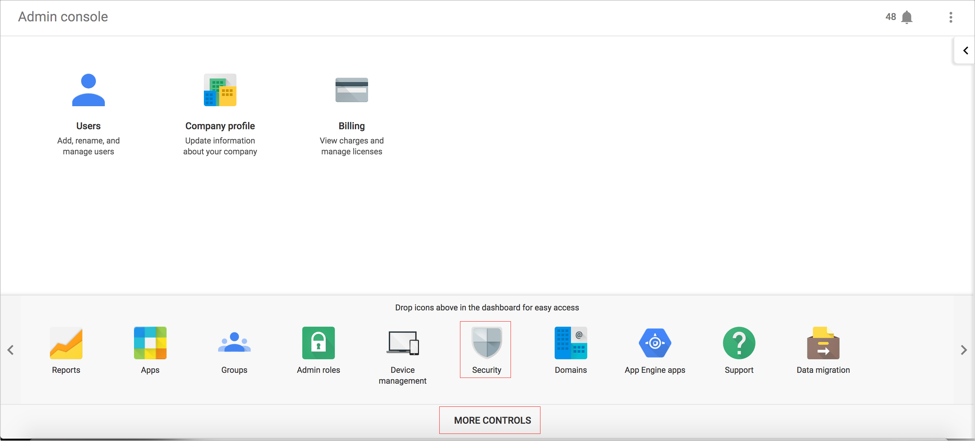
Click the Security icon, as shown here:

Note: If the Security icon is not visible, click More Controls at the bottom of the panel and drag the Security icon into the Admin Console dashboard:
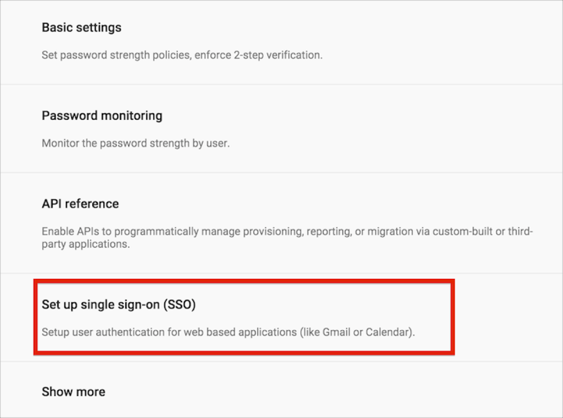
On the Security menu, select Set up single sign-on (SSO):
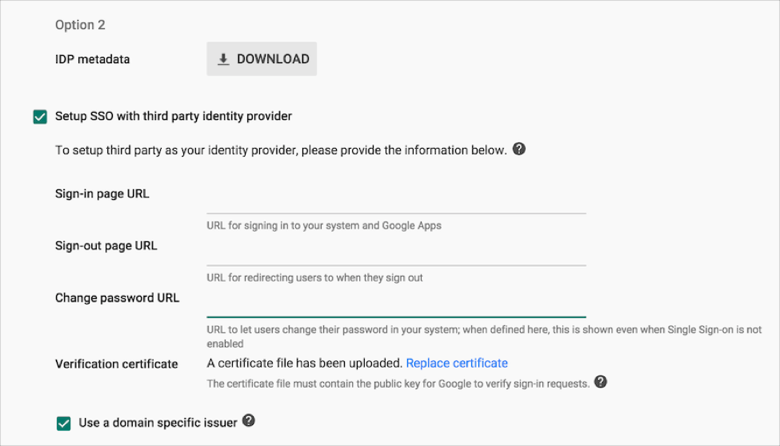
Check Enable Setup SSO with third party identity provider (Option 2), then enter the following (see screen shot at end of document for reference):
Sign-in page URL: Copy and paste the following:
Sign into the Okta Admin Dashboard to generate this variable.
Sign-out page URL: Copy and paste the following:
Sign into the Okta Admin dashboard to generate this value.
Change Password URL: Copy and paste the following:
Sign into the Okta Admin dashboard to generate this value.
Check Use a domain-specific issuer.
(Optional) Use the Network masks field to allow only a targeted subset of users to access your organization's Okta site. This is useful for rolling out application access in controlled phases.
Download your Google verification certificate and then upload it in the Verification certificate section:
Sign into the Okta Admin dashboard to generate this value.
Click Save changes.
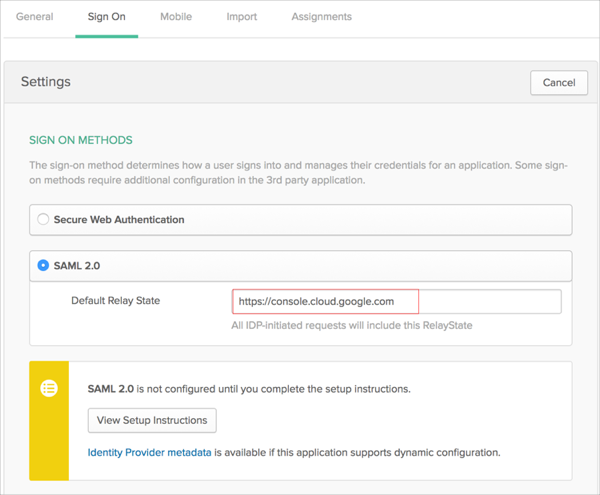
In Okta, select the Sign On tab for the Google Cloud Platform app, then click Edit.
Enter https://console.cloud.google.com in the Default Relay State field.
Click Save changes.
Done!
Navigate to https://www.google.com/a/[DOMAIN]/ServiceLogin?continue=https://console.cloud.google.com.
Where [DOMAIN] is your Google domain.
For example: https://www.google.com/a/acme.com/ServiceLogin?continue=https://console.cloud.google.com